SECURE DEVELOPMENT
Find out how RingCentral's secure development helps ensure product security

Product Security








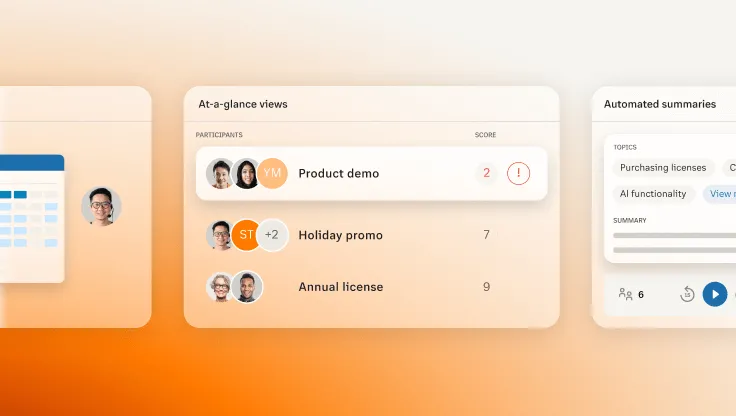
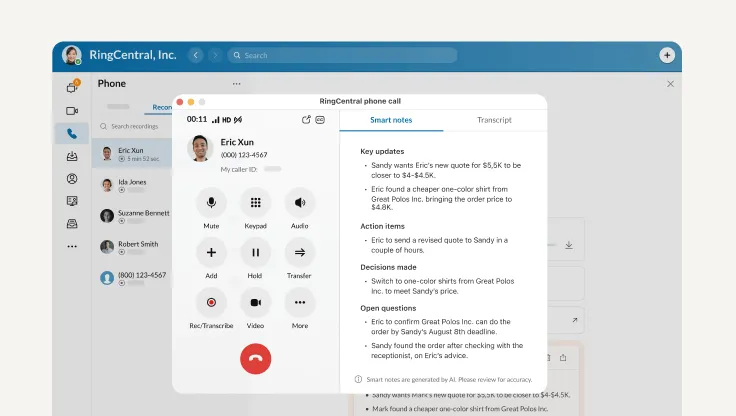
RingCentral’s approach to trustworthy artificial intelligence.
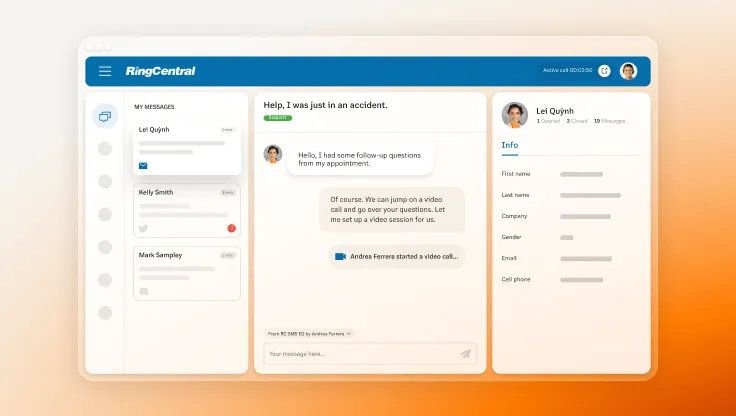
RingCentral products and services comply with data protection laws and regulations around the world.
When RingCentral transfers data we rely on a variety of transfer mechanisms and frameworks.

Webpage

Webpage

Webpage


At RingCentral, trustworthy AI means protecting our customers and their data while maintaining our commitment to privacy, security, and transparency.